Everyone knows how to copy files around using SCP, but it can be a pain if you have to enter passwords for every copy. If you have an administration host with shared ssh keys to every other host, you can just use a quick little one liner to drag files from hostA, through the admin box, over to hostB:
adminbox # ssh hostA "tar cf - /usr/local/sbin/myscript.sh 2>/dev/null" | ssh hostB "cd / && tar xvf - 1>/dev/null"Using tar, the file is output to STDOUT and piped over ssh, then read from STDIN. It copies /usr/local/sbin/myscript.sh from hostA to hostB. Because the admin box has ssh keys to both hostA and hostB, the process is automatic and does not require password authentication. This means you can use this method in scripts for batch copies, etc. Also, you won’t have to create a temporary copy on the admin host.
Drop it into a simple shell script and it will be even easier:
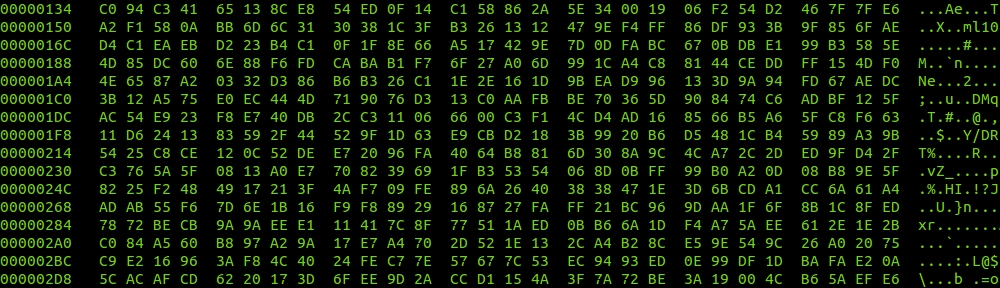
#!/bin/bash # FILE: file_dragger.sh # AUTHOR: fordodone <fordodone at email.com> # DATE: 2013/07/11 # NOTES: drags a file from one host to another # if [ $# -ne 3 ] then echo "" echo "usage: </full/path/to/file> <src> <dst>" echo "" exit fi ssh $2 "tar cf - $1 2>/dev/null" | ssh $3 "cd / && tar xvf - 1>/dev/null"
To use it for the original copy example do this:
# file_dragger.sh /usr/local/sbin/myscript.sh hostA hostB
#